JSON Web Token (JWT) is an open standard (RFC 7519) that defines a compact
and self-contained way for securely transmitting information between parties as
a JSON object. This information can be verified and trusted because it is
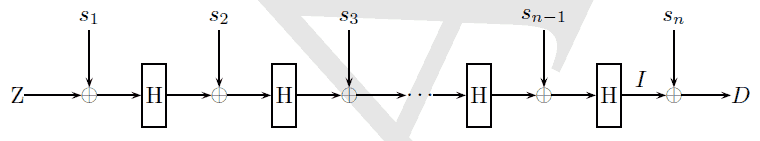
digitally signed. JWTs can be signed using a secret (with the HMAC algorithm)
or a public/private key pair using RSA or ECDSA.
They can be used for:
- Authentication: including a
JWTto any HTTP request allows Single Sign On user validation across different domains; - Secure Information Exchange: a small amount of data can be stored in the JWT payload, and is digitally signed to ensure its provenance and integrity.
See http://jwt.io for an introduction to JSON Web Tokens.
Our mORMot framework now implements JWT:
HS256(HMAC-SHA256) andES256(256-bit ECDSA) algorithms (with the addition of the"none"weak algo);- Validates all claims (validation dates, audiences, JWT ID);
- Thread-safe and high performance (2 µs for a
HS256verification under x64), with optional in-memory cache if needed (e.g. for slowerES256); - Stand-alone and cross-platform code (no external
dll, works with Delphi or FPC); - Enhanced security and strong design - per instance, it is by design immune from https://auth0.com/blog/2015/03/31/critical-vulnerabilities-in-json-web-token-libraries
- Full integration with the framework.






.jpg)