
We are pleased to announce the release of mORMot 2.1.
The download link is available on github.
The mORMot family is growing up.
2023-08-24
2023-08-24. Open Source › mORMot Framework

We are pleased to announce the release of mORMot 2.1.
The download link is available on github.
The mORMot family is growing up.
2021-11-16
2021-11-16. Open Source › mORMot Framework

EKON 25 at Düsseldorf was a great conference (konference?).
At last, a physical gathering of Delphi developers, mostly from Germany, but also from Europe - and even some from USA! No more virtual meetings, which may trigger the well known 'Abstract Error' on modern pascal coders.
There were some happy FPC users too - as I am now.

I have published the slides of my conferences, mostly about mORMot 2.
By the way, I wish we would be able to release officially mORMot 2 in December, before Christmas. I think it starts to be stabilized and already known to be used on production. We expect no more breaking change in the next weeks.
2021-08-17
2021-08-17. Open Source › mORMot Framework
Last weeks, we have enhanced mORMot support to one of the more powerful AARM64 CPU available: the Ampere Altra CPU, as made available on the Oracle Cloud Infrastructure.
Long story short, this is an amazing hardware to run on server side, with performance close to what Intel/AMD offers, but with almost linear multi-core scalability. The FPC compiler is able to run good code on it, and our mORMot 2 library is able to use the hardware accelerated opcodes for AES, SHA2, and crc32/crc32c.
2021-02-22
2021-02-22. Open Source › mORMot Framework

Why OpenSSL? OpenSSL is the reference library for cryptography and secure TLS/HTTPS communication. It is part of most Linux/BSD systems, and covers a lot of use cases and algorithms. Even if it had some vulnerabilities in the past, it has been audited and validated for business use. Some algorithms […]
2021-02-13
2021-02-13. Open Source › mORMot Framework

Last week, I committed new ASM implementations of our AES-PRNG, AES-CTR and AES-GCM for mORMot 2.
They handle eight 128-bit at once in an interleaved fashion, as permitted by the CTR chaining mode. The aes-ni opcodes (aesenc aesenclast) are used for AES process, and the GMAC of the AES-GCM mode is computed using the pclmulqdq opcode.
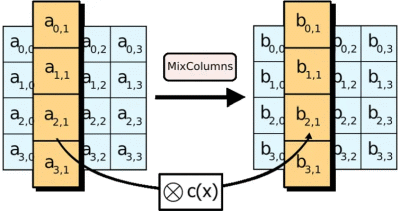
Resulting performance is amazing: on my simple Core i3, I reach 2.6 GB/s for aes-128-ctr, and 1.5 GB/s for aes-128-gcm for instance - the first being actually faster than OpenSSL!
2021-02-12
2021-02-12. Open Source › mORMot Framework
I have just committed some new AesNiHash32 AesNiHash64 AesNiHash128 Hashers for mORMot 2. They are using AES-NI and SSE4.1 opcodes on x86_64 and i386. This implementation is faster than the fastest SSE4.1 crc32c and with a much higher usability (less collisions). Logic was extracted from the Go […]
2020-06-05
2020-06-05. Open Source › mORMot Framework

About latest SQlite3 3.32.xxx there is a big problem with codecs.
Critical changes to the public SQLite code were introduced on Feb 7, 2020: “Simplify the code by removing the unsupported and undocumented SQLITE_HAS_CODEC compile-time option”. With the release of SQLite version 3.32.0 on May 22, 2020 these changes finally took officially effect, although they weren't officially announced.

As a sad and unexpected consequence, we are NOT ANY MORE able to compile the new SQlite3 amalgamation with our encryption patch.
2018-03-12
2018-03-12. Open Source › mORMot Framework
We just committed a deep refactoring of the SynSQlite3Static.pas unit - and all units using static linking for FPC. It also includes a new encryption format for SQlite3, using AES, so much more secure than the previous one. This is a breaking change, so worth a blog article! Now all static .o .a […]
2016-04-09
2016-04-09. Open Source › mORMot Framework
Everyone knows about the pascal random()
function.
It returns some numbers, using a linear
congruential generator, with a multiplier of 134775813,
in its Delphi implementation.
It is fast, but not really secure. Output is very predictable, especially if
you forgot to execute the RandSeed()
procedure.

In real world scenarios, safety always requires random numbers, e.g. for
key/nonce/IV/salt/challenge generation.
The less predictable, the better.
We just included a Cryptographically
Secure Pseudo-Random Number Generator (CSPRNG) into our
SynCrypto.pas unit.
The TAESPRNG class would use real system entropy to generate
a sequence of pseudorandom bytes, using AES-256, so returning highly
unpredictable content.
2015-04-06
2015-04-06. Open Source › mORMot Framework

When publishing SOA services, most of them are defined as
stateless, in a typical query/answer pattern - see
Service-Oriented Architecture (SOA).
This fits exactly with the RESTful approach of Client-Server
services via interfaces, as proposed by the framework.
But it may happen that a client application (or service) needs to know the state of a given service. In a pure stateless implementation, it will have to query the server for any state change, i.e. for any pending notification - this is called polling.

Polling may take place for instance:
It may therefore sounds preferred, and in some case necessary, to have the ability to let the server notify one or several clients without any prior query, nor having the requirement of a client-side timer:
Our mORMot framework is therefore able to easily implement
asynchronous callbacks over WebSockets,
defining the callbacks as interface parameters in service method
definitions - see
Available types for methods parameters.
2015-01-15
2015-01-15. Open Source
Today, we committed a new patch to enable AES-NI hardware acceleration to our SynCrypto.pas unit. Intel® AES-NI is a new encryption instruction set that improves on the Advanced Encryption Standard (AES) algorithm and accelerates the encryption of data on newer processors. Of course, all this is […]